Action1 Features
Administration (8)
Usage Information
Offers visibility into employee device activity
Integrations
Allows for integration of support, chat, diagnostic or other IT management tools
Diagnostics
Provides administrators with performance information to
Unattended Access
Allows administrators access to devices, regardless of end-user's presence
Screen Sharing
Provides screen sharing options to allow access to view or control real-time activities.
Unattended Remote Access
Provides remote access to computers at any time, without an end-user present.
Multi - Session Handling
Provides multiple technician support simultaneously.
Multi-Monitor Support
Allows users to switch between multiple end users’ monitors with a single click.
Platform (4)
Cross-Platform Access
Allows remote usage and access across a range of operating systems and device types
Mobile Device Access
Allows remote desktop administrators access to connected mobile devices
Applications Management
Centrally manages, configures, and oversees applications on employee devices
Remote Device Control
Allows administators to take control of a connected endpoint device
Security (4)
Remote Wipe
Enable the remote locking down and encryption of employee devices
Device Management
Unifies endpoint management of employee devices
Data Encryption
Implements encryption standards to secure data both in transit and at rest.
Compliance
Provides compliance to multiple industry standards like HIPAA and GDPR.
Inventory Management - Remote Monitoring & Management (RMM) (3)
Device Management
Unifies endpoint management of employee devices
Asset Management
Maintains detailed records of network assets and their activity; detects new assets accessing the network
ITIL Policy Compliance
Supports implementation and adherence to ITIL processes and regulations
Monitoring and Management (5)
Remote Monitoring
Monitor IT asset activity remotely from an administrator terminal.
Asset Tracking
Tracks IT assets and financial data.
Application Deployment
Releases applications for access on desktop or mobile devices.
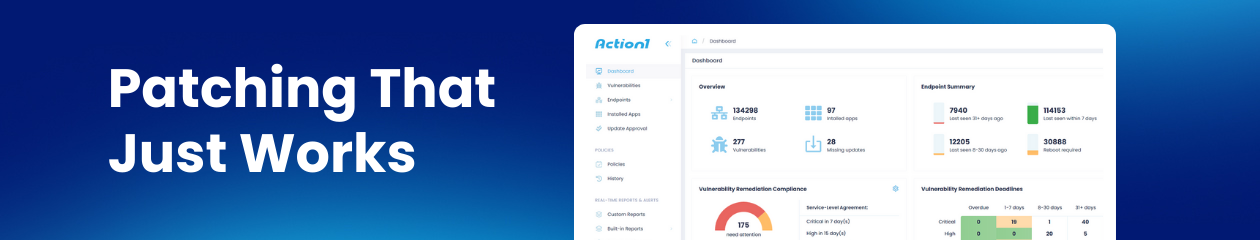
Patch Management
Automates the updating of security measures on enterprise devices.
Asset Tracking
Tracks IT assets including financial and lifecycle data.
IT Operations & Workflow - Remote Monitoring & Management (RMM) (1)
Workflow Management
Enables creation and optimization of workflows for IT support and service delivery
Service Management (3)
Remote Access
Controls access to legacy applications, web based applications, networks resources while employees are outside the local area network.
Service Management (Issue Prioritization)
Analyzes operational data to proactively identify and prioritize IT issues.
Ticketing
Provides tools for creating and managing support tickets across departments
Maintenance (1)
Remote Reboot
Remotely wake, restart, and install applications on sleeping devices.
Device Support (2)
Mobile Device Access
Allows mobile device access to provide support or connect to your computer from anywhere.
Multi-Platform Support
Provides support across iOS, Mac, Android, PC and other devices.
Performance (1)
Reporting
Provides robust reporting capbilities like session details, technician performance information, and end users’ survey summaries.
Agentic AI - Remote Monitoring & Management (RMM) (7)
Autonomous Task Execution
Capability to perform complex tasks without constant human input
Multi-step Planning
Ability to break down and plan multi-step processes
Cross-system Integration
Works across multiple software systems or databases
Adaptive Learning
Improves performance based on feedback and experience
Natural Language Interaction
Engages in human-like conversation for task delegation
Proactive Assistance
Anticipates needs and offers suggestions without prompting
Decision Making
Makes informed choices based on available data and objectives
Generative AI - Autonomous Endpoint Management (3)
Behavioral Analysis
Creates detailed models of normal user and device behavior across endpoints.
Adaptive
Generates new security policies or modifies existing ones to adapt to evolving threats.
Predictive
Analyze patterns and predicts potential endpoint failures or security breaches before they occur to proactively perform maintenance tasks or apply security patches, reducing downtime and preventing incidents.
Monitoring and Management - Autonomous Endpoint Management (4)
Patch Management
Automatically deploys software updates and security patches to ensure all endpoint devices remain up-to-date with the latest protection against vulnerabilities.
Oversees
Automatically discovers and maintains an updated inventory of all endpoints within the network, ensuring accurate asset management.
Self-Healing
Equips endpoints with the ability to self-diagnose and repair certain issues without manual intervention.
Centralized Dashboard
Provides centralized monitoring of endpoint status and health, enabling remote troubleshooting and management for IT teams.