Multi-Factor Authentication (MFA) Software Resources
Articles, Glossary Terms, Discussions, and Reports to expand your knowledge on Multi-Factor Authentication (MFA) Software
Resource pages are designed to give you a cross-section of information we have on specific categories. You'll find articles from our experts, feature definitions, discussions from users like you, and reports from industry data.
Multi-Factor Authentication (MFA) Software Articles
What is Multi-Factor Authentication (MFA)? Types and Benefits
What Multi-Factor Authentication (MFA) Software Users Told Us: Summer 2022
Ranking Multi-Factor Authentication (MFA) Software Based on G2 Reviews
Two-Factor Authentication: A Valuable Addition to Account Security
What Is Single Sign-on? How It Makes Authentication Simple
How FIDO Standards Make Authentication Simple and Secure
2021 Trends in Cybersecurity
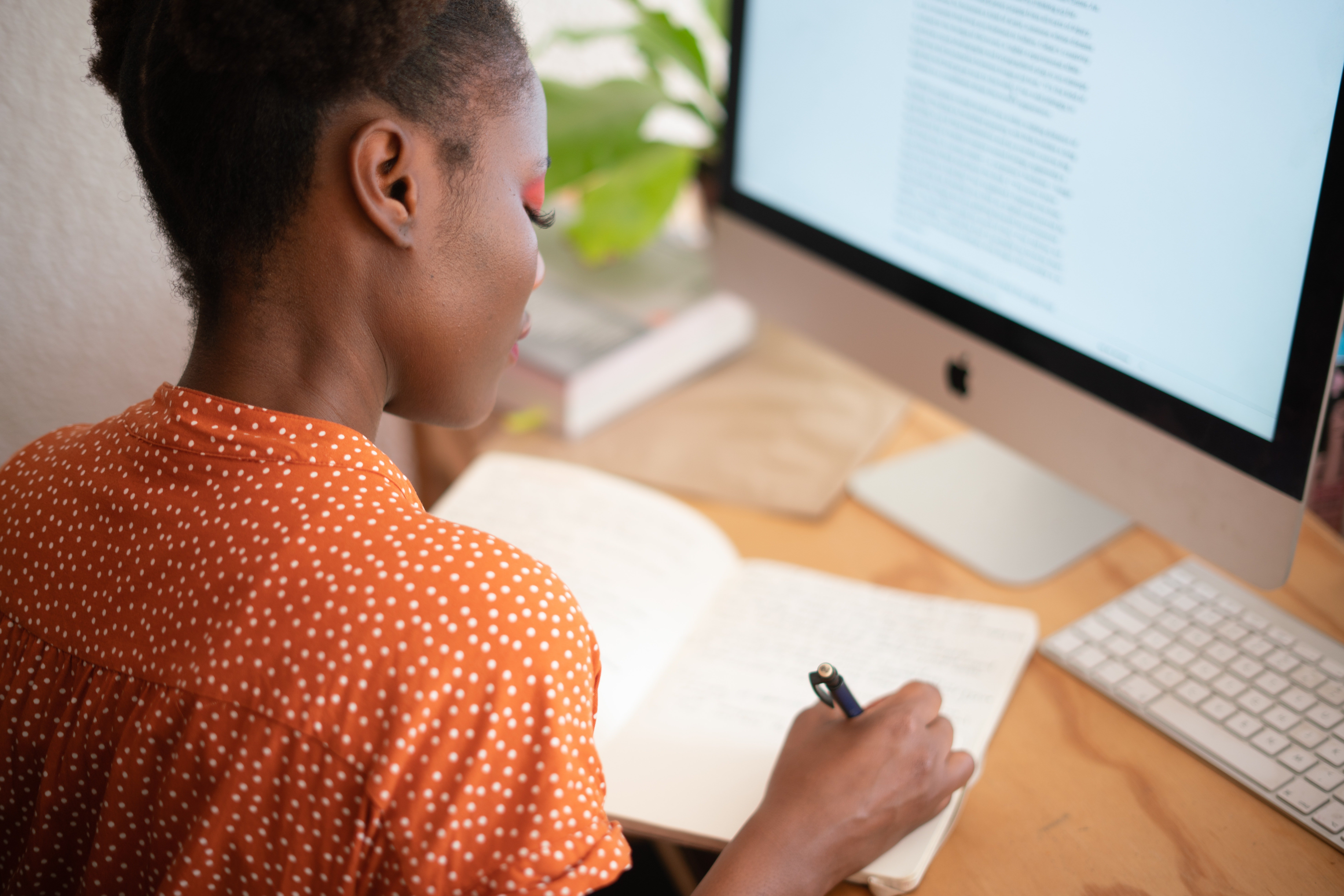
User Adoption is the Key to Calculating ROI for Security Solutions
Infographic: How to Secure a Remote Workforce
COVID-19 Spawns Security Concerns For Rapidly Expanding, Under-Protected Workforce
The Ultimate Guide to Passwordless Authentication
Analyzing API Security in the Multicloud World
Challenges of Multicloud Solution Management and Security
Multi-Factor Authentication (MFA) Software Glossary Terms
Multi-Factor Authentication (MFA) Software Discussions
I am unsure if this is already an option available to us as Enterprise users. If it is available, how do I take advantage of it. If it is not available, could we not set something like this up. There is a competing product that leverages a connection to the "Have I Been Pwned" database.
because if I do not like the application and I do not have the way to recover the authentication key of google, because when asking the company for the disablement, they should place in the middle of the verification measures the recovery of the unique key