Multi-Factor Authentication (MFA) Software Resources
Articles, Glossary Terms, Discussions, and Reports to expand your knowledge on Multi-Factor Authentication (MFA) Software
Resource pages are designed to give you a cross-section of information we have on specific categories. You'll find articles from our experts, feature definitions, discussions from users like you, and reports from industry data.
Multi-Factor Authentication (MFA) Software Articles
What is Multi-Factor Authentication (MFA)? Types and Benefits
Consider how much of your life takes place on a computer or a mobile device.
by Alexa Drake
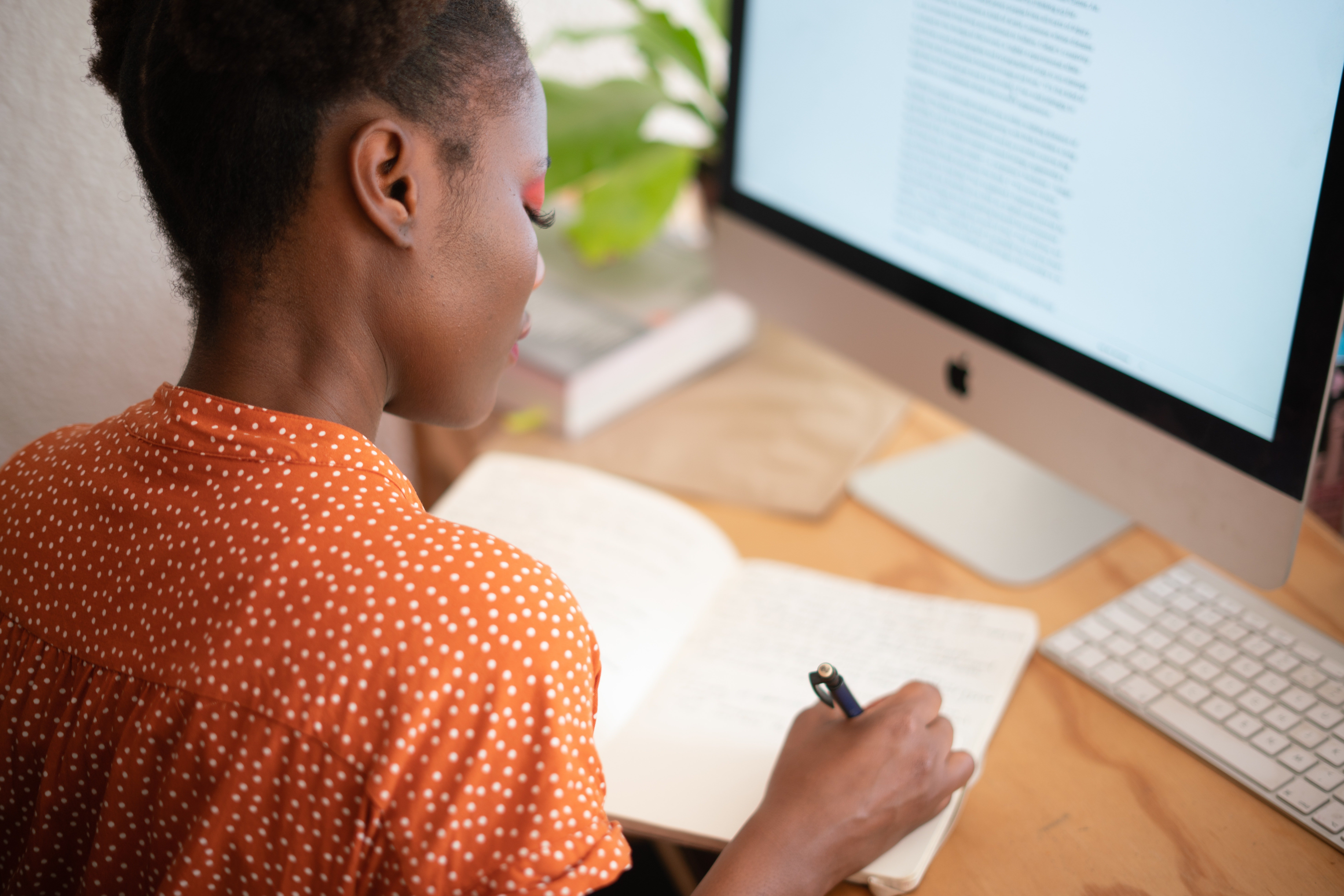
What Multi-Factor Authentication (MFA) Software Users Told Us: Summer 2022
The users of multi-factor authentication (MFA) software products have spoken. They’ve told us in MFA product reviews what they like, what they dislike, information about their implementations, the price, and more. I’ve analyzed the latest user review data that G2 has for the Multi-Factor Authentication category, which is based on MFA software user reviews through May 31, 2022. I picked the data points that would be of most interest to current MFA users and potential MFA buyers.
by Merry Marwig, CIPP/US
Ranking Multi-Factor Authentication (MFA) Software Based on G2 Reviews
Single-factor authentication, such as inputting a username and password to sign in to an account, is an outdated and insecure method of authenticating a user. Passwords can be and often are hacked and misused. Most modern companies require multi-factor authentication (MFA) to access user or business accounts for increased security. MFA software requires end users to authenticate their identity in two or more ways before granting access.
by Merry Marwig, CIPP/US
Two-Factor Authentication: A Valuable Addition to Account Security
Humans are predictable. Sometimes, so are their passwords.
by Sagar Joshi
What Is Single Sign-on? How It Makes Authentication Simple
Time is a precious commodity.
by Sagar Joshi
How FIDO Standards Make Authentication Simple and Secure
Fast identity online (FIDO) standards are authentication protocols where security and user experience meet.
by Sagar Joshi
2021 Trends in Cybersecurity
This post is part of G2's 2021 digital trends series. Read more about G2’s perspective on digital transformation trends in an introduction from Michael Fauscette, G2's chief research officer and Tom Pringle, VP, market research, and additional coverage on trends identified by G2’s analysts.
by Aaron Walker
User Adoption is the Key to Calculating ROI for Security Solutions
The return on investment (ROI) is impossible to calculate for cybersecurity solutions. For such solutions, value isn’t found through dollars saved or deals closed; value is found in unobstructed disaster avoidance and a sense of trust for employees, partners, and customers.
by Aaron Walker
Infographic: How to Secure a Remote Workforce
The COVID-19 pandemic has wreaked havoc across the world, impacting nearly every individual and business. As a result, many companies have shifted their operations to adapt to working remotely, in order to align with social distancing requirements.
by Aaron Walker
COVID-19 Spawns Security Concerns For Rapidly Expanding, Under-Protected Workforce
Worldwide, social distancing has affected the day-to-day activities of nearly every person. In many cases, that means working from home.
by Aaron Walker
The Ultimate Guide to Passwordless Authentication
You have business accounts, therefore you have usernames and passwords...for now.
by Merry Marwig, CIPP/US
Analyzing API Security in the Multicloud World
Modern applications send and receive an unfathomable amount of data at any given time. This flow of data is powered through application programming interfaces (APIs).
by Aaron Walker
Challenges of Multicloud Solution Management and Security
Not all clouds are created equal, at least not in terms of security.
by Aaron Walker
Multi-Factor Authentication (MFA) Software Glossary Terms
Multi-Factor Authentication (MFA) Software Discussions
0
Question on: Daon
Can Daon reduce AI-driven risk around remote hiring?Can Daon reduce AI-driven risk around remote hiring?
Show More
Show Less
xProof counters synthetic identities, AI-generated resumes, credential fabrication, and impersonation at, or before, the point of hire by leveraging liveness detection for both documents and candidates, validating identity and work related documents against 350+ fraud indicators, matching identity documents to live biometric face scans, and cross-checking extracted data against authoritative external sources.
Show More
Show Less
0
Does Daon's workforce identity solution integrate with our existing HR systems?
Show More
Show Less
Yes. Daon integrates with Oracle HCM, Workday HCM, and SAP SuccessFactors via OIDC and API. The solution is aligned with the U.S. Accountability Through Electronic Verification Act and the U.K. Economic Crime and Corporate Transparency Act, as well as other emerging employee identity regulations globally.
Show More
Show Less
0
Question on: Daon
How does Daon address employee identity risk for businesses?How does Daon address employee identity risk for businesses?
Show More
Show Less
Daon's workforce identity solution covers the full employee lifecycle under the Know Your Employee (KYE) framework. At hiring, or during the interview process, xProof verifies the candidate's government-issued ID with a face scan including liveness, spoofing, and tampering checks. Employment documents, including right-to-work credentials and qualifications are ingested and validated. At the completion of the IDV process, a biometric template can be stored and a passkey generated from the selfie captured. xFace leverages the biometric template for strong authentication when adding credentials, for step-up authentication of high-risk activities such as adding authorized devices or payroll account changes, and to address any risk-signals that are detected. Ongoing account maintenance includes scheduled low-friction reverification and continual risk monitoring.
Show More
Show Less
Multi-Factor Authentication (MFA) Software Reports
Mid-Market Grid® Report for Multi-Factor Authentication (MFA)
Spring 2026
G2 Report: Grid® Report
Grid® Report for Multi-Factor Authentication (MFA)
Spring 2026
G2 Report: Grid® Report
Enterprise Grid® Report for Multi-Factor Authentication (MFA)
Spring 2026
G2 Report: Grid® Report
Momentum Grid® Report for Multi-Factor Authentication (MFA)
Spring 2026
G2 Report: Momentum Grid® Report
Small-Business Grid® Report for Multi-Factor Authentication (MFA)
Spring 2026
G2 Report: Grid® Report
Enterprise Grid® Report for Multi-Factor Authentication (MFA)
Winter 2026
G2 Report: Grid® Report
Small-Business Grid® Report for Multi-Factor Authentication (MFA)
Winter 2026
G2 Report: Grid® Report
Mid-Market Grid® Report for Multi-Factor Authentication (MFA)
Winter 2026
G2 Report: Grid® Report
Grid® Report for Multi-Factor Authentication (MFA)
Winter 2026
G2 Report: Grid® Report
Momentum Grid® Report for Multi-Factor Authentication (MFA)
Winter 2026
G2 Report: Momentum Grid® Report