Cloud Security Software Resources
Articles, Glossary Terms, Discussions, and Reports to expand your knowledge on Cloud Security Software
Resource pages are designed to give you a cross-section of information we have on specific categories. You'll find articles from our experts, feature definitions, discussions from users like you, and reports from industry data.
Cloud Security Software Articles
CASB vs. SSE: Which Cloud Security Solution is Right for You?
Cloud Storage Security: How to Keep Your Cloud Data Safe?
AWS re:Invent 2021 Roundup: A G2 Perspective
An Amazonian Challenge: The Year of Cloud Partnerships
Cloud Computing in Health Care
Analyzing API Security in the Multicloud World
Challenges of Multicloud Solution Management and Security
G2 on Cloud Security: Investigating the Risks of Cloud Computing
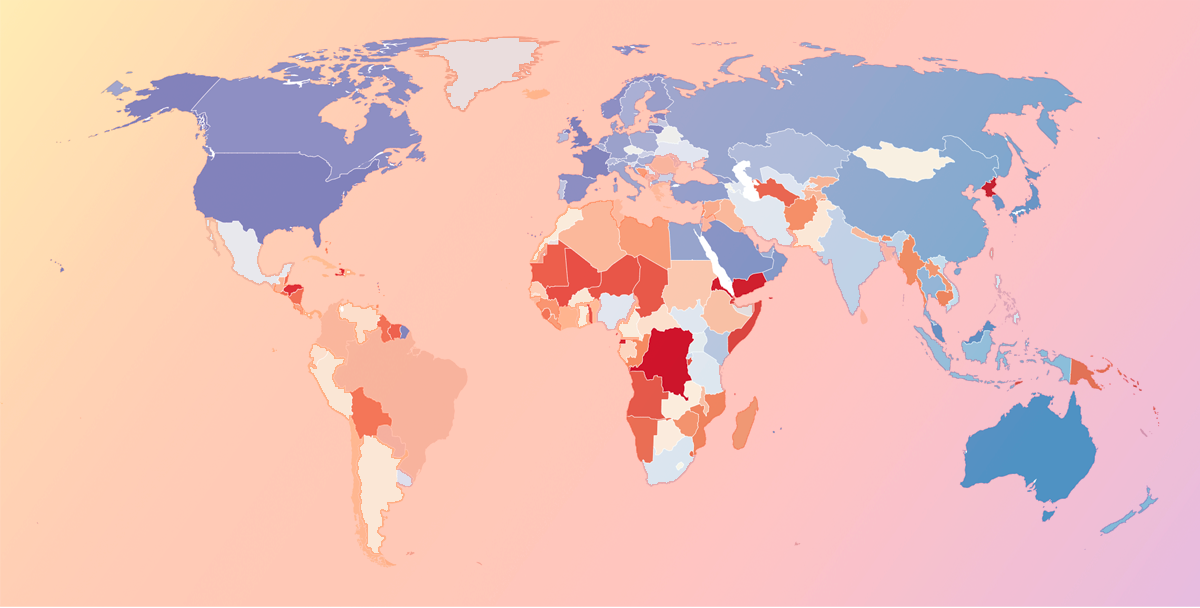
National Cybersecurity and Popular Products Across the World
Cloud Security Software Glossary Terms
Cloud Security Software Discussions
Even with containers growing fast, VMs still run critical business workloads. CWPPs protect VM workloads by scanning for vulnerabilities, monitoring behavior, and detecting malware/abuse in runtime.
We’re currently exploring:
- Microsoft Defender for Cloud – for native VM protections and posture management, especially in Azure/hybrid setups.
- Orca Security – for agentless VM scanning and detection of malware, vulnerabilities, and sensitive data risks.
- Check Point CloudGuard Network Security – for VM-adjacent network segmentation and threat prevention.
Which of these tools would you best recommend?
What’s been most useful: vuln management, hardening, or runtime defense?
Real-time workload protection is a core CWPP promise — especially for catching active attacks in cloud runtimes. CWPPs are designed for continuous monitoring and detection across workloads.We’re currently exploring:
- Sysdig Secure – known for real-time runtime detection using Falco rules and deep container/Kubernetes visibility.
- CrowdStrike Falcon Cloud Security – for continuous workload monitoring and detection across modern cloud stacks.
- SentinelOne Singularity Cloud Security – for autonomous detection/response for cloud workloads.
- FortiCNAPP – for behavioral anomaly detection in cloud workloads.
- Which tools give the fastest, most accurate runtime alerts?
- How noisy are detections in real environments?
Have you used any of these tools? Which ones would you best recommend?
Any standout response workflows that reduce MTTR?
For organizations in regulated spaces (finance, healthcare, public sector), CWPPs need to do more than detect threats — they must also support continuous compliance, policy enforcement, and audit-ready reporting across cloud workloads.
We’re currently exploring:
- Wiz – for unified workload visibility, risk prioritization, and compliance-aligned controls.
- Sysdig Secure – for runtime detection plus compliance coverage across Kubernetes/container workloads.
- Orca Security – for broad workload risk detection (vulns, malware, sensitive data) with agentless reach.
- Hybrid Cloud Security (Trend Micro) – for hybrid workload protection and compliance posture across environments.
- Microsoft Defender for Cloud – for native Azure/hybrid compliance tooling and workload protection.
We’re curious:
- Which CWPPs are most effective for audit preparation and continuous compliance?
- Any gaps you’ve seen in policy enforcement or compliance reporting?
Have you used any of these tools? Which one would you best recommend?
What features matter most in regulated environments (certifications, templates, evidence trails)?