Cloud Data Security Software Resources
Articles, Glossary Terms, Discussions, and Reports to expand your knowledge on Cloud Data Security Software
Resource pages are designed to give you a cross-section of information we have on specific categories. You'll find articles from our experts, feature definitions, discussions from users like you, and reports from industry data.
Cloud Data Security Software Articles
What Is Cloud Security? Understanding the Basics of Cloud
When a business decides to move its data into the cloud, there is always the underlying question of security.
by Mara Calvello
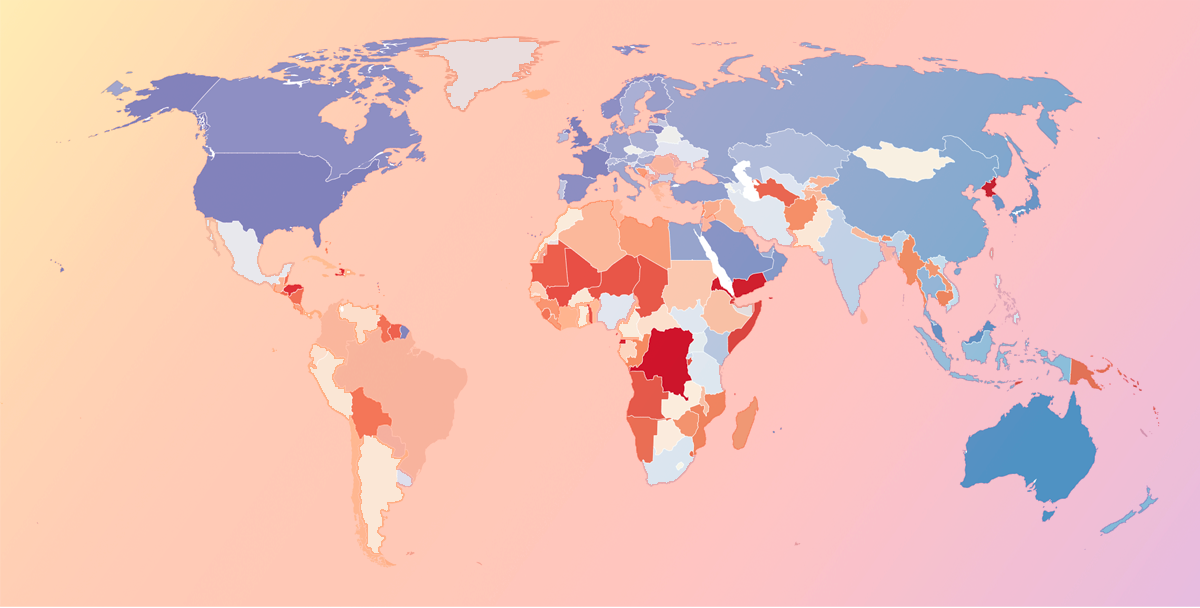
National Cybersecurity and Popular Products Across the World
In a digital age, data security is a top priority, but it can be difficult to know who exactly is responsible for securing sensitive information. While companies may feel they have sufficiently secured their own data, those that utilize SaaS vendors in their business put their sensitive information and business data in the hands of these vendors, who store it in the cloud or on-premises at their location.
There are a number of security considerations and variables a business should keep in mind, especially related to cloud security. But it's helpful to remember one simple question when considering vendors or evaluating current protection efforts: Does the country housing my data care about security?
Countries that do have taken action to protect personal and business data stored in their country or region. Other efforts to protect personal information include enforcing security standards, developing national cybersecurity strategies, and providing public awareness campaigns, among others. Countries that received lower scores have done less to ensure businesses are protecting data and require less transparency between data collectors and individuals.
In a globalized world, servers could be housed in any number of countries other than the one your business or a software vendor operates in. Still, it should be considered a potential red flag if vendors operate out of extremely vulnerable geographical regions.
Every year, the International Telecommunication Union (ITU) releases the results of a worldwide security survey titled the United Nations Global Cybersecurity Index (CGI). The index provides an overall security rating based on a number of factors related to legislative, organizational, technical, capacity building, and international cooperation.
by Aaron Walker
Cloud Data Security Software Glossary Terms
Explore our Technology Glossary
Browse through dozens of terms to better understand the products you purchase and use everyday.
Cloud Data Security Software Discussions
0
Question on: nOps
What are some of nOps cost optimization features?
What are the tools nOps are offering for optimizing costs and how does it different from other platforms?
Show More
Show Less
With nOps, you can:
Track infrastructure costs by project, AWS and Azure account, resource & employee.
Get real-time notifications of billing anomalies, across all regions & services.
Instantly view infrastructure changes that affect cost.
Identify underutilized resources and do smarter RI & Spot Instances Planning.
Rightsize Instances - analyze instances continuously to determine optimum sizes.
Maximize Your Amazon EC2/RDS Reserved Instance Spend with ShareSave risk-free commitment management.
Show More
Show Less
0
I would need bit more clarity on the pricing model. Thanks:)
Show More
Show Less
nOps pricing model is unique in that you only pay for what you save. We are the first cloud management platform that charges based on a fraction of the customer's savings - which means no more cloud tax. Our incentives are aligned to optimize your AWS costs.
You can find more information on our pricing here: https://www.nops.io/pay-only-for-what-you-save/
Show More
Show Less
0
Question on: Check Point Harmony Email & Collaboration
What are the different types of email security?
What are the different types of email security?
Show More
Show Less
Email security is crucial when it comes to protecting our data privacy from cyber attacks and security breaches.
We can implement multiple layers of security enhancements to preserve our customer-sensitive information.
1. SPF implementation - Sender Policy Framework effectively enables the owners of the domain to scrutinize which servers are authorized to send emails & verify its authenticity.
2. Malware scanner utilities - It is helpful to scan our email attachments & associated links for malicious & suspicious contents to stop it from entering into our system.
3. Content Filtering Policies - They are used when we need to report or block emails containing sensitive elements & offensive contexts. Its also used to preserve our security standards and to prevent any data leakages.
Show More
Show Less
Several types of email security measures that can be implemented to protect against various threats. Here are some of the most common types of email security:
Antivirus/Anti-malware: This type of security software scans incoming and outgoing emails for viruses and other malware, such as Trojan horses, spyware, and ransomware.
Spam filters: These filters are used to block unwanted and unsolicited emails, also known as spam, from reaching the inbox. They are designed to identify and block emails with suspicious content or from unknown senders.
Content filters: These filters are used to monitor email content for specific keywords or phrases that may indicate a security threat, such as credit card numbers, social security numbers, or other sensitive information.
Encryption: Email encryption is a security measure that protects the confidentiality of email messages by scrambling the content of the message so that only the intended recipient can read it.
Authentication: Email authentication is the process of verifying the identity of the sender of an email message. Common email authentication methods include SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting and Conformance).
Two-factor authentication (2FA): 2FA is an additional layer of security that requires users to provide two forms of identification to access their email account, such as a password and a security token or biometric identification.
By implementing one or more of these email security measures, businesses can help protect against a range of email-based threats, including phishing attacks, malware, spam, and data breaches.
Show More
Show Less
Cloud Data Security Software Reports
Mid-Market Grid® Report for Cloud Data Security
Spring 2026
G2 Report: Grid® Report
Grid® Report for Cloud Data Security
Spring 2026
G2 Report: Grid® Report
Enterprise Grid® Report for Cloud Data Security
Spring 2026
G2 Report: Grid® Report
Momentum Grid® Report for Cloud Data Security
Spring 2026
G2 Report: Momentum Grid® Report
Small-Business Grid® Report for Cloud Data Security
Spring 2026
G2 Report: Grid® Report
Enterprise Grid® Report for Cloud Data Security
Winter 2026
G2 Report: Grid® Report
Small-Business Grid® Report for Cloud Data Security
Winter 2026
G2 Report: Grid® Report
Mid-Market Grid® Report for Cloud Data Security
Winter 2026
G2 Report: Grid® Report
Grid® Report for Cloud Data Security
Winter 2026
G2 Report: Grid® Report
Momentum Grid® Report for Cloud Data Security
Winter 2026
G2 Report: Momentum Grid® Report